
Six Steps to Deploying Zero Trust Today
A Practical Guide to Continuous Verification with WatchGuard
Explore Zero Trust SecurityMove zero trust from vision to execution:
- Reduce risk across identity, device, and access with clear priorities
- Modernize remote access without adding complexity or friction
- Build a zero trust strategy that scales as your business grows
Zero trust built on continuous verification, least-privilege access, and adaptive policies that follow users wherever they go.
From Perimeter to Policy. The perimeter is gone.
Users connect from everywhere – homes, airports, and shared networks.
Applications live in SaaS platforms and hybrid clouds. Attackers exploit stolen credentials, unmanaged devices, and over-privileged VPNs to infiltrate networks undetected.
The solution isn’t another tool.
It’s a new security mindset: zero trust built on continuous verification, least-privilege access, and adaptive policies that follow users wherever they go.
This guide outlines six practical steps to deploy zero trust today by unifying identity security, endpoint security, hybrid network security, and extended threat detection and response under one cloud-managed policy control plane.
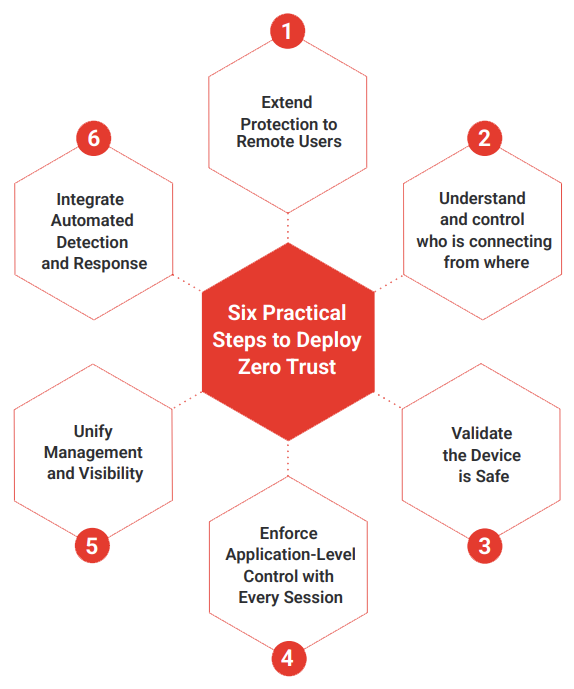
Table of Contents
- Protect Users:
Even Beyond the Network - Verify Identity:
Who Is Connecting and From Where? - Validate the Device:
What Is Connecting? - Enforce Session-Level Access:
What Are They Reaching? - Unify Management and Visibility:
How Do You See and Control It All? - Integrate Automated Detection and Response:
How Do You Respond in Real Time? - The Payoff:
Zero Trust Without Boundaries

